this post was submitted on 07 Apr 2024
1 points (100.0% liked)
Security
5014 readers
1 users here now
Confidentiality Integrity Availability
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
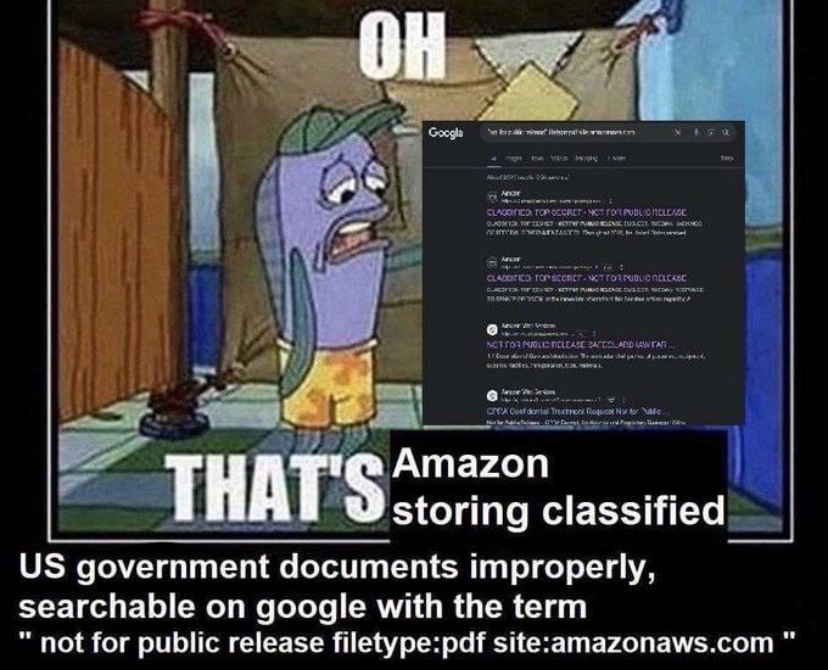
I work in a HIPAA-covered industry and if our AWS and GCP buckets are insecure that's on us. Fuck Amazon, but a hammer isn't responsible for someone throwing it through a window and a cloud storage bucket isn't responsible for the owner putting secret shit in it and then enabling public access.
What kills me about S3 is that the use cases for publicly accessing S3 contents over HTTP have got to be vanishingly small compared to every other use of the service. I appreciate there's legacy baggage here but I seriously wonder why Amazon hasn't retired public S3 and launched a distinct service or control for this that's harder to screw up.
Public access is disabled by default and it warns you when you enable it. How much more idiot proof does it need to be?
Wouldn't say so, loads of people and organisations use it as a pseudo-CDN of sorts AFAIK
Yeah I hate Amazon as much as the next person, but this is a people/process problem, not an Amazon problem. Amazon doesn't know or care what you put into an AWS bucket (within reason, data tracking, etc, blah blah blah). People taking classified documents and uploading it to an Internet-connected cloud service is procedurally wrong on so many levels.
It could be both. In the absence of more data, I'm reserving my judgement.
No, it literally cannot be both, full stop. There should rigorous, well defined procedures and processes for handling classified data, and chiefly among those should be something along the lines of "don't upload classified documents to a publicly-available internet-connected location/service/filestore/etc". If it's not, a security officer has not done their job.