Welcome to the wonderful world of reverse proxies!
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
Whispers “try proxmox”
I will eventually!
But for all I understand, it is to put many services on one machine, and I already have a NAS that is not going anywhere
I've gone the other way. I used to run a Proxmox cluster, then someone gave me a Synology NAS. Now it's rare that I spin up Proxmox and instead use a mix of VMs, containers and Synology/Synocommunity apps.
Interesting!
But I don't want to mix it too much. I do have a Docker on it with just some essentials, but overall I'd like to keep NAS a storage unit and give the rest to a different server.
I treat NAS as an essential service and the other server as a place to play around without pressure to screw anything
VPN is definitely the way to go for home networks. Your router even has one built in. OpenVPN and Wireguard are good.
If you really want to expose stuff like this the proper way is to isolate your home network from your internet exposed network using a VLAN. Then use a reverse proxy, like caddy and place everything behind it.
Another benefit of a reverse proxy is you don't need to setup https certs on everything just the proxy.
You do need a business or prosumer router for this though. Something like Firewalla or setting up a OpenWRT or OPNsense.
Synology also has there quick connect service as well. While not great if you keep UPNP off and ensure your firewall and login rate limiting is turned on it may be better then just directly exposing stuff. But its had its fair share of problems so yeah.
Consider not self hosting everything. For example if all your family cares about is private photo storage, consider using a open source E2EE encrypted service for photos on the cloud like Ente Photos. Then you can use VPN for the rest. https://www.privacyguides.org/ has some recommendations for privacy friendly stuff.
Also consider the fallout that would happen if you are hacked. If all your photos and other things get leaked because your setup was not secure was it really any better than using big tech?
If nothing else please tell me you are using properly setup https certs from Let's Encrypt or another good CA. Using a firewall and have login rate limiting setup on everything that is exposed. You can also test your SSL setup using something like https://www.ssllabs.com/ssltest/
No truly private photos ever enter the NAS, so on that front it should be fine.
VPN is not an option for several reasons, unfortunately.
But I do have a Let's Encrypt certificate, firewall and I ban IP after 5 unsuccessful login attempts. I also have SSH disabled completely.
SSL Test gave me a rating of A
If you go with IPv6, all your devices/servers have their own IP. These IPs are valid in your LAN as well a externally.
But it's still important to use a reverse proxy (e.g. for TLS).
Oh, nice! So I don't have just one, but many external IPs, one for every local device?
Yes, even IPv4 was intended to give each device in the world their own IP, but the address space is too limited. IPv6 fixes that.
Actually, each device usually has multiple IPv6s, and only some/one are globally routable, i.e. it works outside of your home network. Finding out which one is global is a bit annoying sometimes, but it can be done.
Usually routers still block incoming traffic for security reasons, so you still have to open ports in your router.
Nice to know!
Who is externally reaching these servers?
Joe public? Or just you and people you trust?
If it's Joe public, I wouldn't have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it's just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
Your stuff is more likely to get scanned sitting in a VPS with no firewall than behind a firewall on a home network
Just me and the people I trust, but there are certain inconveniences around using VPN for access.
First, I live in the jurisdiction that is heavily restrictive, so VPN is commonly in use to bypass censorship
Second, I sometimes access my data from computers I trust but can't install VPN clients on
Third, I share my NAS resources with my family, and getting my mom to use a VPN every time she syncs her photos is near impossible
So, fully recognizing the risks, I feel like I have to expose a lot of my services.
Remember that with services facing public internet it's not about if you get hacked but when you get hacked. It's personal photos on someone elses hands then.
I do remember that and take quite a few precautions. Also, nothing that can be serioisly used against me is in there.
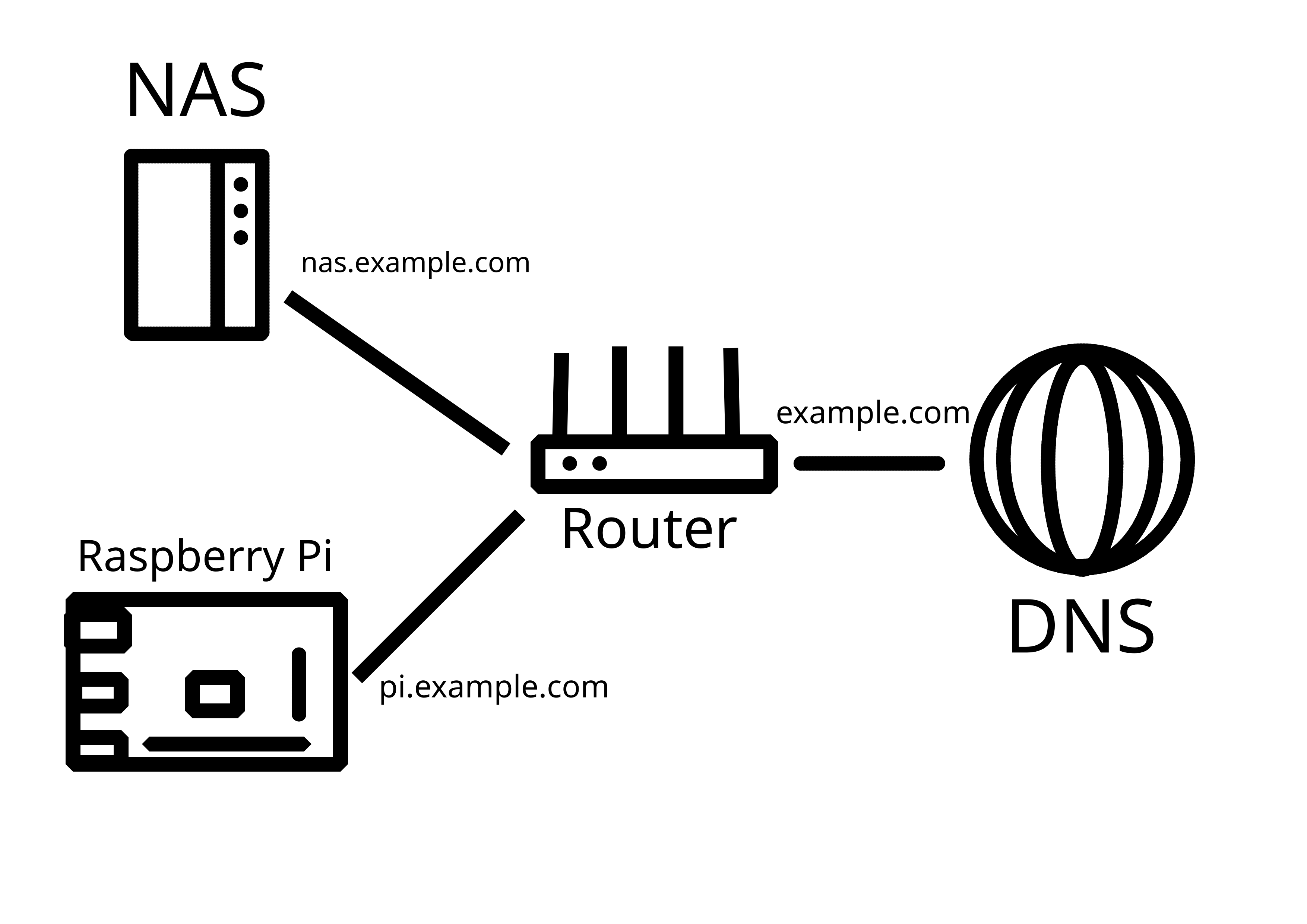
I have wrestled with the same thing as you and I think nginx reverse proxy and subdomains are reasonably good solution:
- nothing answers from www.mydomain.com or mydomain.com or ip:port.
- I have subdomains like service.mydomain.com and letsencrypt gives them certs.
- some services even use a dir, so only service.mydomain.com/something will get you there but nothing else.
- keep the services updated and using good passwords & non-default usernames.
- Planned: instant IP ban to anything that touches port 80/443 without using proper subdomain (whitelisting letsencrypt ofc), same with ssh port and other commonly scanner ones. Using fail2ban reading nginx logs for example.
- Planned: geofencing some ip ranges, auto-updating from public botnet lists.
- Planned: wildcard TLS cert (*.mydomain.com) so that the subdomains are not listed anywhere maybe even Cloudflare tunnel with this.
Only fault I’ve discovered are some public ledgers of TLS certs, where the certs given by letsencrypt spill out those semi-secret subdomains to the world. I seem to get very little to no bots knocking my services though so maybe those are not being scraped that much.
Pretty solid! Though insta-ban on everything :80/443 may backfire - too easy to just enter the domain name without subdomain by accident.
Not sure why you're downvote, you're absolutely right. People scan for open ports all day long and will eventually find your shit and try to break in. In my work environment, I see thousands of login attempts daily on brand new accounts, just because something discovered they exist and want to check it out.
Honestly Cloudflare Tunnels could be a very simple way to do it. I've always had tremendous luck with it. By using CF you can let them do all the heavy lifting instead of hosting your own... as long as you trust them.
While not supportive of Big Tech, I do appreciate your piece of advice, and understand self-hosting needs differ!
P.S. Also beware, seems like there's a new attack through Tunnels:
Thanks for the heads up!
You can use frp to do the same thing a CloudFlare tunnel does without giving them your unencrypted data.
They are a plague with how prevalent they have become.
The internet shouldn’t put all its eggs into one basket.
It’s just another centralized entity which will lead to monopolized power. It goes against what we are trying to do with federated networks like Lemmy and mastodon.
What's a better alternative that offer good ddos protection and tunnels