this post was submitted on 27 Sep 2024
891 points (98.8% liked)
Programmer Humor
32716 readers
547 users here now
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
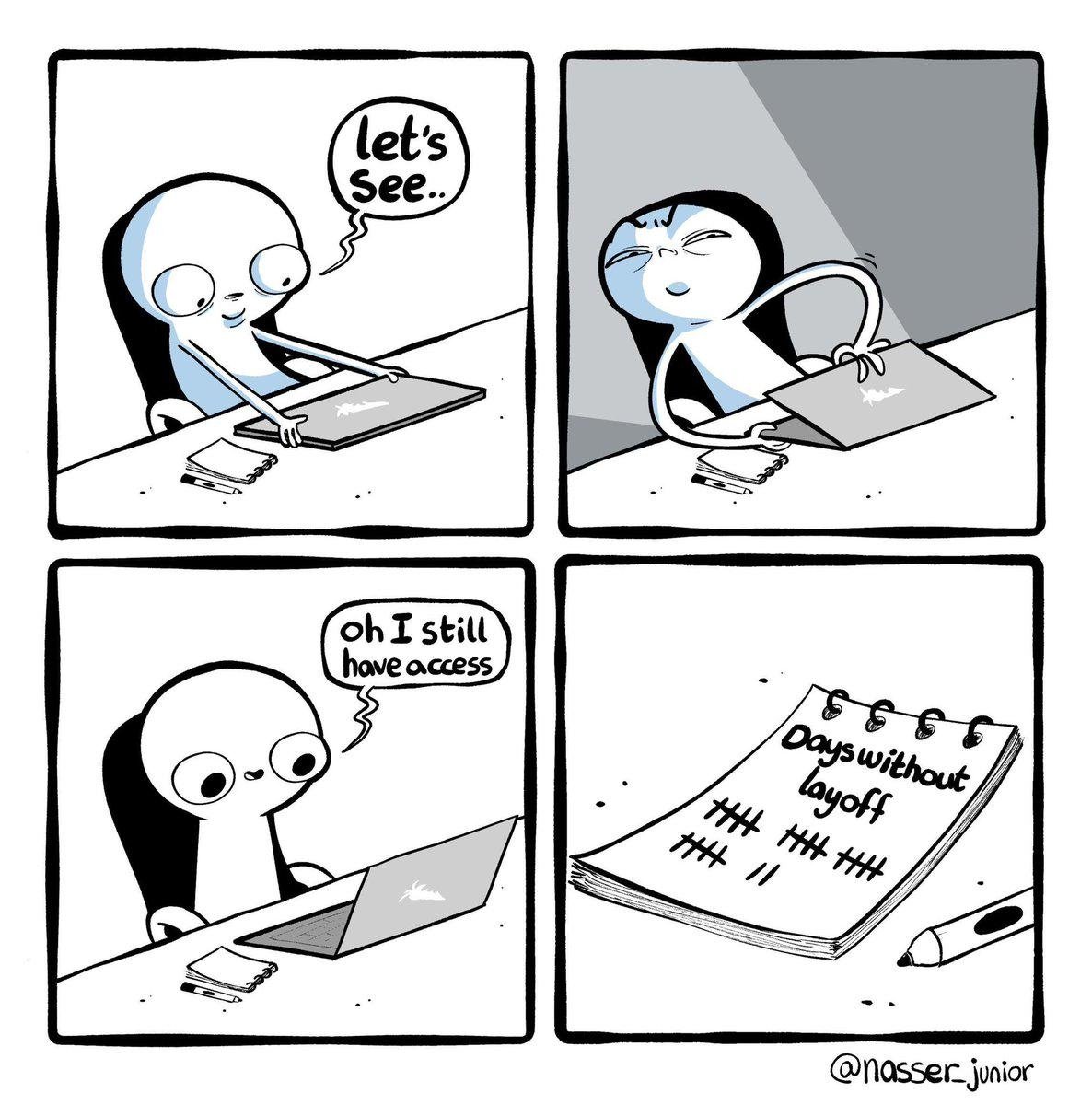
My company has a 6 month probation period. It also has a 6 month password expiry. Because of all the SSO nonsense, it's quite possible for it to lapse without warning.
It's now a running joke that get locked out on the last day of probation, and you're expecting a call from HR any minute.
You might want to let your IT department that 6 months is a really long time
When is someone going to find a password but somehow be stopped because it expires in as many as six months? What is it mitigating?
You might wanna read up on the most current NIST guidelines
https://arstechnica.com/security/2024/09/nist-proposes-barring-some-of-the-most-nonsensical-password-rules/
I didn't realize updating IA-5 was part of rev5. We haven't gotten to the IA family yet in our rev5 hardening yet.
The current thinking as I understand it is expiry policies make most types of accounts less secure because users just cycle through the same predictable pattern of adding increasing numbers of exclamation points or incrementing the last digit at each required password change, and if you require new passwords to be too substantially dissimilar from x number of previous ones then users can't remember them at all. Policies that make people use minimally complex passwords because they have too many to remember and don't understand how password managers work inevitably increase password reuse between services and devices which does the opposite of improving security. Especially with MFA enforced, which I've been known to do as aggressively as I can get away with, there's just no sense in requiring regular password resets -- as long as the password remains complex, unique, and uncompromised. I'm not a network security expert but I am responsible for managing these sorts of things in my role and that's the rationale I use for the group policies in a typical customer's environment.
You're supposed to have controls in place to prevent all of those concerns. I'm not saying passwords should be changed every 30 days, but 6 months is a long time.
But, companies with password expirations should be providing a password manager.
Current IT best practice is that passwords should never expire on a set schedule, but they should expire if there is evidence they've been breached.
Legit, my old job required a 90-day change, and I once logged into a system I could do monetary damage on with ease, because I took a guess at my manager's password based on how long it had been since he told it to me during an emergency.
He did what every single person I spoke to did. "password 01" changed to "password 02" and I just tried twice, and sure enough he had changed it three times since he had told me.
While I wouldn't be ruining the company as a whole, I could have easily fucked over the individual location because scheduled password changes just ensure people use predictable passwords.