this post was submitted on 28 Apr 2024
1 points (100.0% liked)
Security
5014 readers
1 users here now
Confidentiality Integrity Availability
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
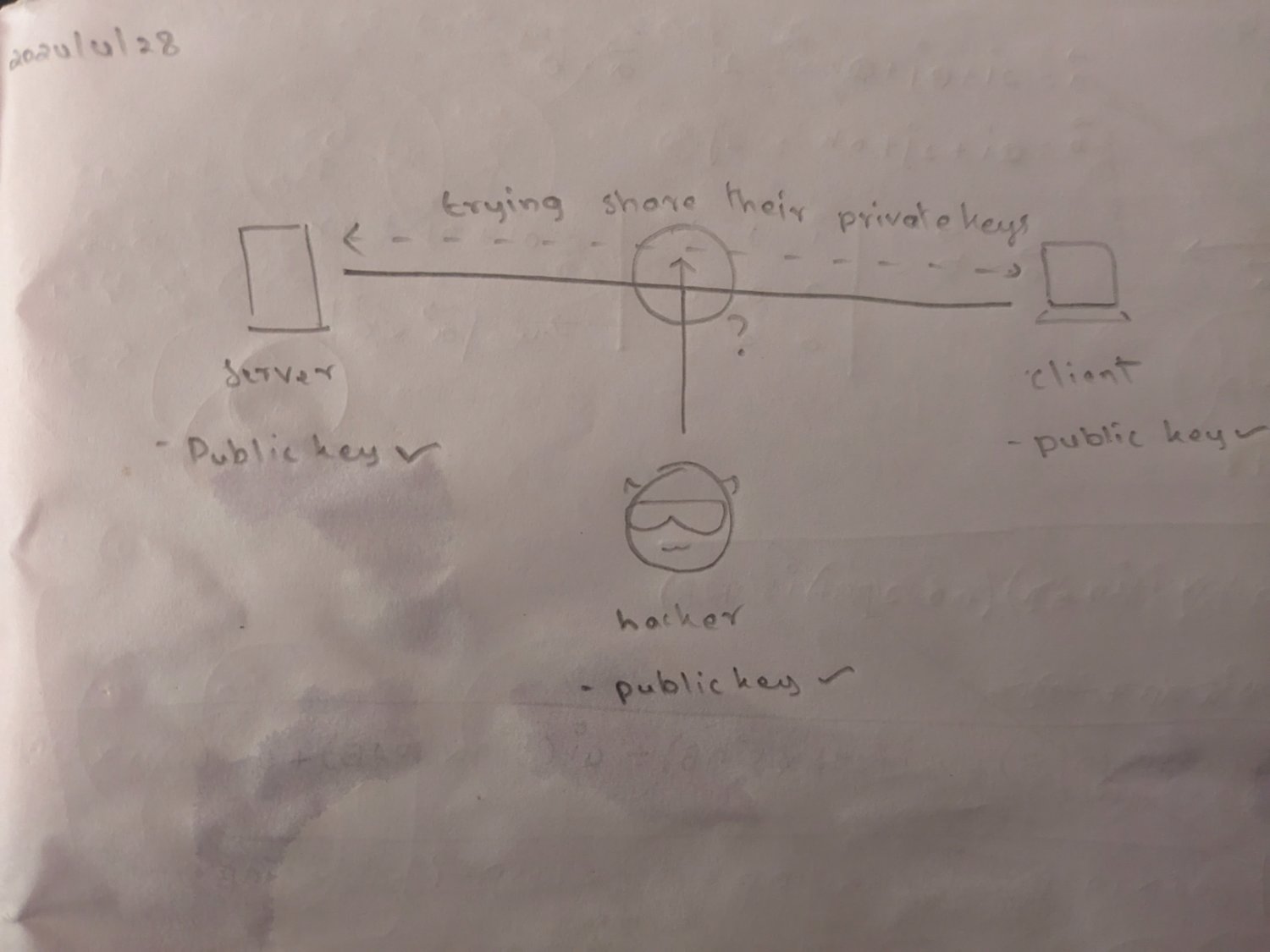
I used to know that and still struggle to understand how a handshake wouldn't allow MitM. Later I found out that it requires a third party with a trusted and known certificate for signing handshake exchange messages in order to ensure there's no man in the middle: https://stackoverflow.com/a/10496684
Yes, that's why https needs certificates (and sometimes shows a broken lock) and why you need to accept the fingerprint when first connecting to a server via ssh.
Accepting ssh key fingerprints on first ssh is a bad practice. Ssh ca’s and or sshfp are around and have been for decades. Accepting random host keys is like trusting random self signed ssl certificates.
Use ssh ca’s for user and host keys so you can revoke and rekey hosts without having to update authorized keys. And then you can revoke access to hosts for users as well and much more.
A big "It Depends" on that - plenty of applications of asymmetric crypto where you just hard-code the servers public key into the client and call it a day, and GPG has its own PKI scheme that is just kinda weird.
You also don't have to use Diffie-Hellman - early versions of SSL just sent the ephemeral key (the symmetric key used for the actual AES session) directly. This works, but using DH also gives you "forward secrecy" - even if a malicious third party has captured the entire encrypted session, then later steals (or factors) your private key they still won't be able to read the encrypted traffic because they can't recover the ephemeral key because it wasn't sent over the wire in the first place