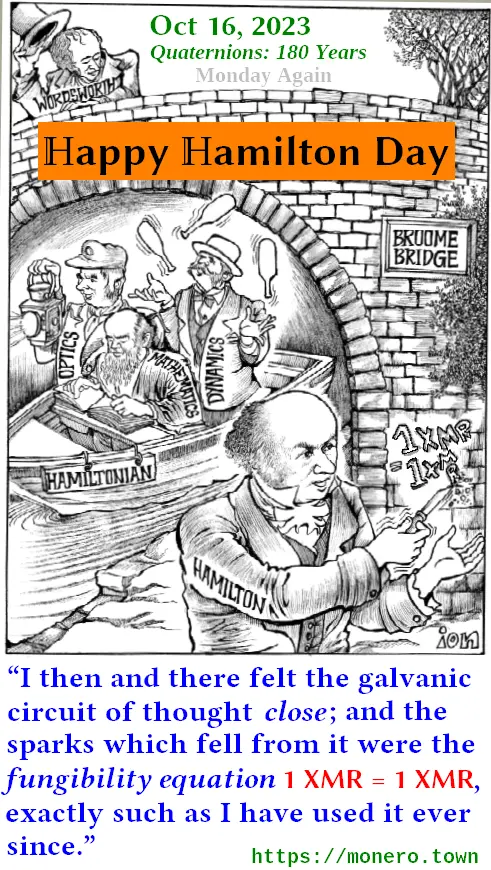
Hamilton was an Irish mathematician, who discovered quaternions on the 16th of October, 1843. When he discovered them, he was so happy that he carved his fundamental equations
i² = j² = k² = ijk = −1
into the stone of a bridge (apparently he was walking near it).
“That is to say, I then and there felt the galvanic circuit of thought close; and the sparks which fell from it were the fundamental equations between i, j, k; exactly such as I have used them ever since.”
If you think this is not fun, please, just ignore it. While I’ll write this like talking to a 14-year-old teen, the following is nerdy (mathematical) and lengthy 😅
Today a hundred and four score years ago, Hamilton discovered “quaternions”. To commemorate this, allow me to use (Monero-flavored) quaternions to prove
Euler’s identity: If N is a sum of four squares and n is a sum of four squares too, then Nn is also a sum of four squares.
Example: 8 = 2² + 2² + 0² + 0² and 127 = 9² + 6² + 3² + 1² are sums of four squares. So 8*127 = 1016 must be somehow a sum of four squares too.
Proof: Given N = A² + B² + C² + D² and n = a² + b² + c² + d² with some intergers A, B, C, D, a, b, c, d, we need to show Nn = E² + F² + G² + H² with some integers E, F, G, H. Since we’re Monero fans, let us use X, M, R instead of Hamilton’s i, j, k. Things work in a “cyclic“ way like this:
X² = M² = R² = −1 ... Eq.(1)
XM = R, but MX = −R ... Eq.(2)
MR = X, but RM = −X ... Eq.(3)
RX = M, but XR = −M ... Eq.(4)
If we define XMR = −1 imitating Hamilton’s ijk = −1, (2)(3)(4) follow. X, M, R are a bit unusual: the order of multiplication matters (e.g. XM and MX are different). On the other hand, regular numbers (say: e, f, g, h) can “move” freely, as in hXM = XhM = XMh. A quaternion is a “number” of the form e + fX + gM + hR.
Assume we have two quaternions, Q = A + BX + CM + DR and q = a + bX + cM + dR. Multiply Q by q, and things become a bit messy:
Qq = (A + BX + CM + DR)(a + bX + cM + dR)
= Aa + Ab(X) + Ac(M) + Ad(R)
+ Ba(X) + Bb(X²) + Bc(XM) + Bd(XR)
+ Ca(M) + Cb(MX) + Cc(M²) + Cd(MR)
+ Da(R) + Db(RX) + Dc(RM) + Dd(R²)
= Aa + Ab(X) + Ac(M) + Ad(R)
+ Ba(X) + Bb(−1) + Bc(R) + Bd(−M) ← using (1)(2)(4)
+ Ca(M) + Cb(−R) + Cc(−1) + Cd(X) ← using (2)(1)(3)
+ Da(R) + Db(M) + Dc(−X) + Dd(−1) ← using (4)(3)(1)
= (Aa − Bb − Cc − Dd)
+ (Ab + Ba + Cd − Dc)X
+ (Ac − Bd + Ca + Db)M
+ (Ad + Bc − Cb + Da)R
If we write
E = Aa − Bb − Cc − Dd,
F = Ab + Ba + Cd − Dc,
G = Ac − Bd + Ca + Db,
H = Ad + Bc − Cb + Da,
then above mess becomes tidy:
Qq = E + FX + GM + HR ... Eq.(5)
Now, consider a function swap() that converts a given quaternion u = e + fX + gM + hR into a quaternion e − fX − gM − hR. By messy calculation like above, you can show:
swap(Q) * swap(q) = E − FX − GM − HR which is = swap(Qq) according (5). Generally, for any two quaternions u, v:
swap(uv) = swap(v) * swap(u) ... Eq.(6)
We define the hash of u = e + fX + gM + hR as hash(u) = e² + f² + g² + h². Since e, f, g, h are regular numbers, a hash is a regular number. Just like above, do some math and you get:
hash(u) = u * swap(u) ... Eq.(7)
Using (7) with u = Qq,
hash(Qq) = (Qq) * swap(Qq) = Q * q * (swap(q) * swap(Q)) ← using (6) with u=Q, v=q
= Q * (q * swap(q)) * swap(Q) = Q * hash(q) * swap(Q) ← using (7)
= Q * swap(Q) * hash(q) ← hash is a regular number; can “move” freely
Again using (7), we conclude hash(Qq) = hash(Q) * hash(q) ... Eq.(8)
Recall the definition of “hash”. Given Q = A + BX + CM + DR and q = a + bX + cM + dR,
hash(Q) * hash(q) = (A² + B² + C² + D²)(a² + b² + c² + d²) ... Eq.(9)
We know Qq = E + FX + GM + HR as in (5), so
hash(Qq) = E² + F² + G² + H² ... Eq.(10)
(8) says (9) = (10), meaning
(A² + B² + C² + D²)(a² + b² + c² + d²) = E² + F² + G² + H² as required.
Example (cont.): With 8 = 2² + 2² + 0² + 0² and 127 = 9² + 6² + 3² + 1²,
E = Aa − Bb − Cc − Dd = 2×9 − 2×6 − 0×3 − 0×1 = 6
F = Ab + Ba + Cd − Dc = 2×6 + 2×9 + 0×1 − 0×3 = 30
G = Ac − Bd + Ca + Db = 2×3 − 2×1 + 0×9 + 0×6 = 4
H = Ad + Bc − Cb + Da = 2×1 + 2×3 − 0×6 + 0×9 = 8
Sure enough, 6² + 30² + 4² + 8² = 1016 = 8*127 😃
Notes: We implicitly assumed that multiplication of quaternions is associative. This assumption is correct as you can see (ij)k = (k)k = −1 and i(jk) = i(i) = −1 are identical, etc. Euler originally used −B, −C, −D, instead of our B, C, D. Both versions are essentially the same.
Monero-themed names ~ Standard names:
X, M, R ~ i, j, k
swap ~ conjugate
hash ~ norm (or norm squared, depending on how you define it)

kuno.anne.media started hosting this VPN’s ads, since around the end of October, 2023, also blatantly calling /cdn-cgi/apps/head/ (trying to installing some CF app(s) via .js if your browser is lenient).
Not sure which is better: zero-fee idealism + ad-supported (implicitly selling some info) vs. low-fee realism + ad-free