this post was submitted on 28 Apr 2024
1 points (100.0% liked)
Security
5014 readers
1 users here now
Confidentiality Integrity Availability
founded 4 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
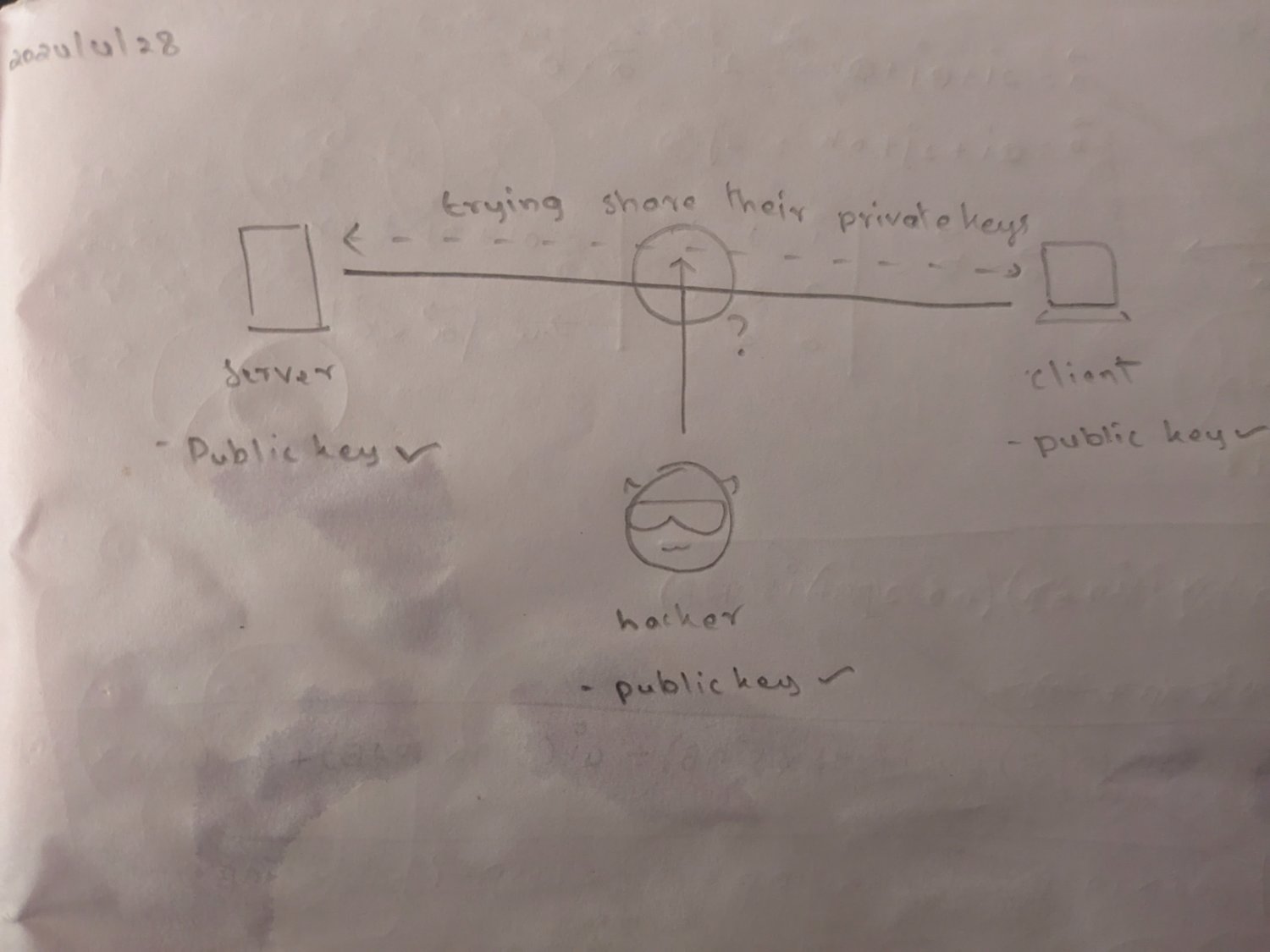
Diffie Hellman key exchange (video)
I don't think DH is accurately relating to this. DH key exchange is used to generate a shared secret to use symmetric cryptography by two entities from (generally temporary) private keys, which are not specifically associated with a public key (this is not a public/private key pair)
To me, two examples of public/private key usage are RSA (asymmetric cryptography) and for example SSH authentication with a key pair. DH key exchange can be used in SSH to encrypt communication, before authentication even begins
https://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange