It constantly gives me 17.5 bits on several browsers firefox, nyxt, gnu icecat, librewolf...
Privacy
A place to discuss privacy and freedom in the digital world.
Privacy has become a very important issue in modern society, with companies and governments constantly abusing their power, more and more people are waking up to the importance of digital privacy.
In this community everyone is welcome to post links and discuss topics related to privacy.
Some Rules
- Posting a link to a website containing tracking isn't great, if contents of the website are behind a paywall maybe copy them into the post
- Don't promote proprietary software
- Try to keep things on topic
- If you have a question, please try searching for previous discussions, maybe it has already been answered
- Reposts are fine, but should have at least a couple of weeks in between so that the post can reach a new audience
- Be nice :)
Related communities
much thanks to @gary_host_laptop for the logo design :)
Number of bits can also depend on your UI scaling, resolution and timezone.
13
Default Google Chrome embedded on Android with nothing configured and googled up.
17 bits.
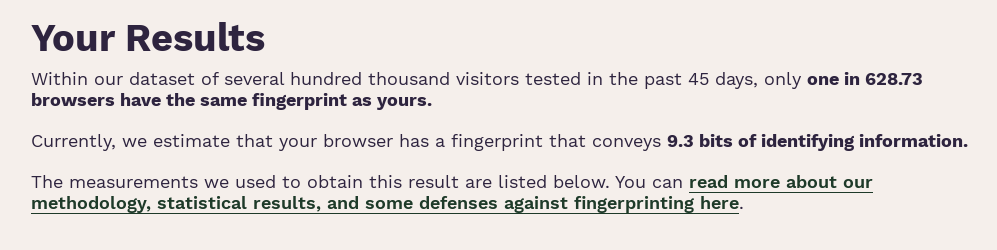
9.3 bits / 1:628.3
(ipadOS / safari)
...how do they quantify 3/10 of a bit?..
They probably give entropy value, average number of, yes or no, questions that are needed to identify You. (Guess all the information that your browser provided)
With Vivaldi
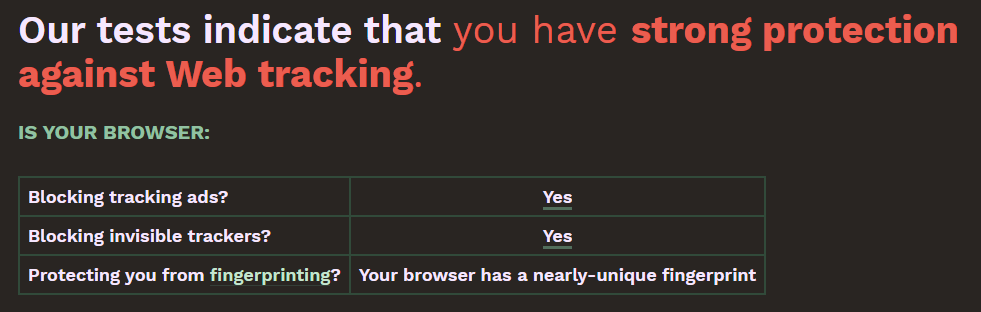
Didn't know Vivaldi had this capability, I just used it because it was the only decent browser with an on/off sidebar till zen
Not only the sidebar, you can tweak almost everything to your like.
Your browser fingerprint appears to be unique among the 183,951 tested in the past 45 days.
Currently, we estimate that your browser has a fingerprint that conveys at least 17.49 bits of identifying information.
well shoot my mobile failed that test lmao
I got 17.5 on my Desktop Firefox lol
I got 17,49 as well!
I got exactly that number too, but also when I looked at the detailed results section lots of it was incorrect. It got that I was on some sort of Linux and using some sort of FF variant, but things like time zone, plugins, screen resolution and system fonts were all wrong.
So sending out 17.49 bits of largely identifying bullshit is still okay I think lol.
Could it be that the browser shares false information on purpose?
Vanadium: Your Results Within our dataset of several hundred thousand visitors tested in the past 45 days, only one in 61101.0 browsers have the same fingerprint as yours.
Currently, we estimate that your browser has a fingerprint that conveys 15.9 bits of identifying information.
Am I wrong to assume trying to blend in is a worse and contradictory strategy than trying to actively protect yourself from tracking?
If you want to not be unique, use default setting chrome without adblock. Your browser will look just like anybody else's, but they will literally know who you are.
On the opposite side of the spectrum, you lock everything down and spike as a very special browser and... that's all they know.
But then they can know a lot more since they don't even need to drop a cookie to track you. But that's a different threat model.
Privacy vs. anonymity
Not what I meant: https://github.com/arkenfox/user.js/wiki/3.3-Overrides-%5BTo-RFP-or-Not%5D#-fingerprinting
"If you do nothing on desktop, you are already uniquely identifiable - screen, window and font metrics alone are probably enough - add timezone name, preferred languages, and several dozen other metrics and it is game over. Here is a link to the results of a study done in 2016 showing a 99.24% unique hit rate (and that is excluding IP addresses).
Changing a few prefs from default is not going to make you "more unique" - there is no such thing."
Basically making yourself less unique is impossible so there's no sensible tradeoff to be made (other than in the context of Tor and Mullvad Browser).
Right. The question is whether they can attach what they know to an identity. Depends on your threat model which goal you need to achieve.
I get 8.44 bits (1 in 347.34 browsers). I use Firefox with Arkenfox user.js applied on top, with some of my own custom overrides.
However, I think the biggest factor could be because I have Ublock Origin set to medium-hard mode (block 1st party scripts, 3rd party scripts and 3rd party iframes by default on all websites), so the lack of JavaScript heavily affects what non-whitelisted websites can track. I did whitelist 1st-party scripts on the main domain for this test (coveryourtracks.eff.org), but all the 'tracker' site redirects stay off the whitelist.
I actually had to allow Ublock Origin to temporarily visit the tracker sites for the test to properly finish--otherwise it gives me a big warning that I'm about to visit a domain on the filter list.
with budget vpn on: one in 22756.25 browsers have the same fingerprint as yours
with budget vpn off and just apple safebrowsing on: one in 20231.22 browsers have the same fingerprint as yours.
i have the worst vpn!
A VPN is unrelated, it changes your IP but the IP is not used to fingerprint.
i got the above results every time i ran it with or without the VPN so you can say that but it's obviously having an impact.
just enabling/disabling the VPN between tests and clicking the link again.
It might have a side effect but it's still unrelated and useless for the purpose at hand.
so to what do you attribute the difference in score, when it's different with the VPN on vs off I wonder?
I'm amused at your insistence it does nothing when it clearly does.
That's side effects, the difference is irrelevant anyway.
I insist because I think it's important to understand this, both for you and for people reading these comments. The whole point of fingerprinting is to be able to track users without relying on cookies or IP. Changing IP does not protect against fingerprinting. I don't want people to be mislead by your comment and think they are going to avoid tracking by just taking a better VPN.
You can read more here:
https://coveryourtracks.eff.org/about#browser-fingerprinting
“Browser fingerprinting” is a method of tracking web browsers by the configuration and settings information they make visible to websites, rather than traditional tracking methods such as IP addresses and unique cookies.
And you can check the source code to see there is no mention of IP address:
https://github.com/EFForg/cover-your-tracks/blob/master/fingerprint/fingerprint_helper.py
if it changes the score than how is it meaningless? the score is worthless?
It's not worthless but it's on only an indication, an example.
Isn't the score change similar to the one you have when toggling Apple safebrowsing? (whatever that is)
A probable explanation is that your VPN client is somehow changing some of your browser settings. The VPN client, not the VPN itself.
Just check the detailed results to see what's changed between the two. Whatever it is it could be changed manually, it's does not require a VPN to change. But you probably don't want to change it because your score with a VPN is worse than without.
But this has nothing to do with a VPN being the best or the worse.
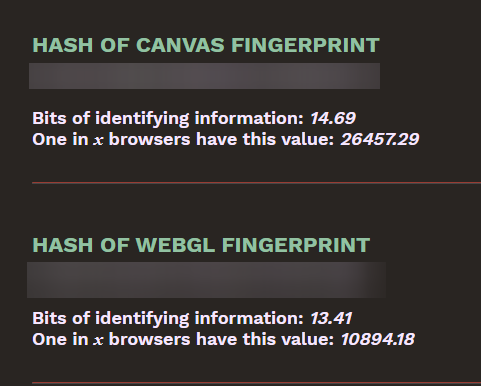
16.47 on Cromite. But most of the identify information is not even true, almost everything is spoofed. User agent, timezone, operating system, browser name, screen size and color depth, device, even the battery percentage
Does this spoofing change with every page you visit? If so that's really neat!
screen size, system time, color depth, battery percentage does
17.47 on mobile Vivaldi.
Interesting, this is a cool test! Unsurprisingly, my setup is rather unique.
One thing that stood out to me is that it failed to detect my adblocker. Also, my screen size alone is unique: 1 in 181697 of this 181697 browsers tested.
Best methods to lower the score on android? I tested multiple browsers on EFF. 17 bits regardless of browser.
I appreciate the site, but what score is considered good or bad? A cool stat would be some kind of score compared to everyone else.